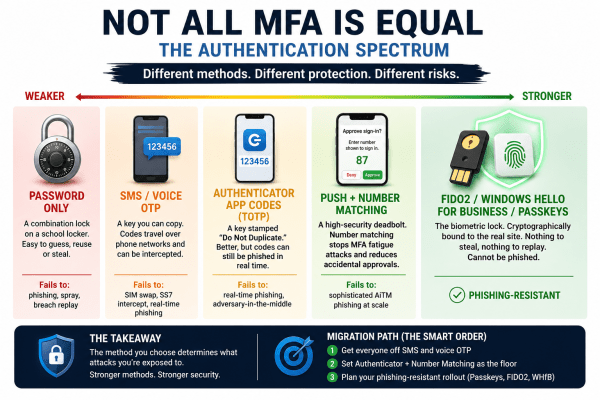
Most MFA setups are not equally secure. Different authentication methods sit on a spectrum, from easily phished passwords and SMS codes to phishing-resistant passkeys and FIDO2 security. This visual breaks down how each method actually fails in real-world attacks, and why the strongest options eliminate entire attack categories instead of just reducing risk.
Passkeys: Strong Security That Only Works If People Actually Use It
Passkeys are a stronger, passwordless way to log in, but their real impact depends on one thing: people actually using them. Until adoption becomes the default, security improvements will remain limited.
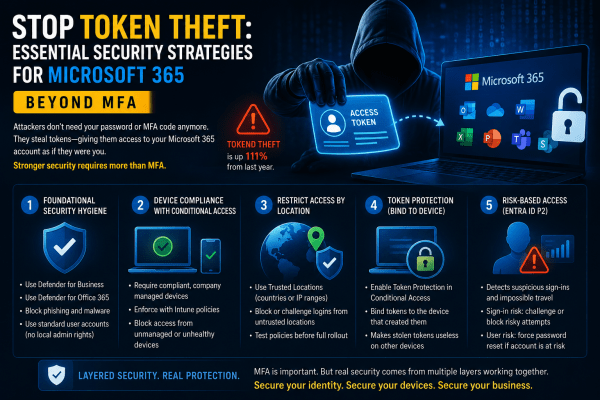
Stop Token Theft: Why MFA Alone Is No Longer Enough for Microsoft 365
Most businesses believe MFA is enough to protect Microsoft 365 accounts. It isn’t. Attackers are now bypassing traditional authentication by stealing session tokens directly from user devices, giving them silent access to emails, files, and company data without triggering MFA prompts. In this article, we break down how token theft works, why it’s becoming one of the fastest-growing cyber threats, and the practical Microsoft 365 security strategies every organization should implement before it becomes a real incident.
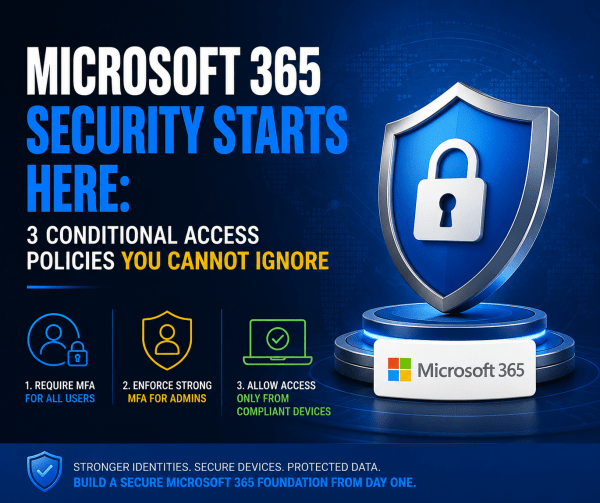
Microsoft 365 Security Starts Here: 3 Conditional Access Policies You Cannot Ignore
Most Microsoft 365 tenants are far less secure than organizations think. A password policy and a basic country block are not enough to stop modern attacks. This article breaks down the three Conditional Access policies every tenant should deploy from day one: strong MFA for all users, phish-resistant authentication for administrators, and device compliance enforcement through Intune. These foundational controls dramatically reduce the risk of account compromise, unauthorized access, and unmanaged devices accessing corporate data.
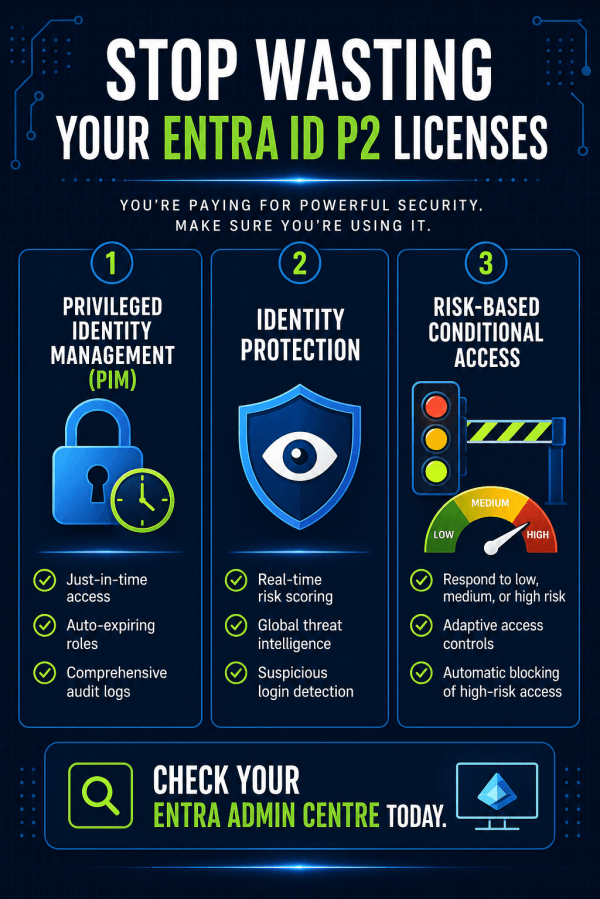
You’re Paying for Entra ID P2 – So Why Aren’t You Using It?
Most teams buy Entra ID P2, assign the licenses, and never touch the premium features. That's thousands wasted and your tenant left exposed. Here's how to actually use what you're paying for.
Understanding Intune’s Compliance Misleading Defaults
Most Intune environments look secure. Green ticks everywhere. Compliant devices. No obvious issues. But here’s the reality: a default setting can mark devices as compliant even when no policies are applied. No encryption checks. No OS validation. No real protection. That “secure” environment? It’s often just a dashboard illusion. If you’re relying on compliance without enforcing it through Conditional Access, you’re not controlling access, you’re just hoping nothing goes wrong. This post breaks down where it fails and how to fix it properly.
The Ultimate Guide to Secure BYOD: Mastering App Protection Policies Instead of Full Device Enrollment
BYOD offers flexibility, but it can also open the door to serious data risks if it’s not managed properly. Instead of taking full control of employees’ personal devices, modern security focuses on protecting the data itself. In this guide, you’ll learn how to secure company information on personal phones using Microsoft Intune App Protection Policies and Conditional Access, giving your team the freedom to work anywhere while keeping sensitive data locked down.
Secure Microsoft 365 Tenants Before Deploying Copilot: A Guide for MSPs
Clients are rushing to deploy Microsoft 365 Copilot, but most tenants are not ready. Weak security, inconsistent policies, and poor configuration can turn AI into a serious risk. Before you roll out Copilot, you need a secure, standardised foundation. Here’s how to protect your clients and position your MSP as the trusted expert.
Automated Identity Defense: Smarter Conditional Access with Risk Remediation
High-risk user alerts at 3 a.m. are exhausting and dangerous. By the time an admin investigates, an attacker may already have full access to email, files, and sensitive data. Microsoft Entra ID changes that with Require Risk Remediation in Conditional Access. Instead of just sending alerts, it automatically blocks compromised accounts and forces secure recovery before access is restored. No delays. No ticket backlog. Just immediate containment and smarter identity protection for Microsoft 365.
Stop Treating All Data the Same: How to Master Microsoft 365 Security with Authentication Contexts
Not all data is equally sensitive, yet many Microsoft 365 environments treat every file and app the same. Blanket multi-factor authentication creates fatigue, and security signals get ignored. That’s where authentication contexts come in. They let you apply stricter Conditional Access controls only to high-value resources—like finance or HR data—while keeping everyday workflows smooth. With granular protection, MFA fatigue drops, security becomes meaningful again, and your most critical data stays safe without slowing down the organization.